Keynote Speakers
Marie Moe
Marie Moe is a Senior Consultant at Mandiant and has a PhD in information security. She is also a part-time Associate Professor at the Norwegian University of Science and Technology where she teaches cyber incident response and has been supervising several students on ethical hacking projects. She is known for hacking her own pacemaker and is currently collaborating with clinicians on digital health research as an honorary visiting senior researcher at Imperial College London.
Elisa Costante
In this talk, Elisa will share the lessons learned in in 10+ years of experience in IoT security. She will discuss how IoT security started, its evolution, the main challenges we face, the similarities and differences with ‘standard’ IT security and how things can look like in the near future
Elisa Costante is the VP of Threat Research at Forescout. In her role, she leads the activities of Vedere Labs, a team of cyber security researchers focused on vulnerability research, threat analysis and threat mitigation. She has 10+ years of experience in the security challenges posed by the IT/OT/IoT convergence. In her prior role she was CTO at SecurityMatters, where she led product innovation activities in the field of network intrusion detection. Elisa holds a PhD in Cyber Security from the Eindhoven University of Technology where she specialized in machine learning techniques for data leakage detection.
Talks
André Lima
In this presentation, I will go through details of not only things to consider when developing in the kernel but, most importantly, things to consider when developing malware for the Windows kernel. I’ll explain synchronization when the Operating System is not cooperating with you, Direct Kernel Object Manipulation (DKOM), and show a demo on injecting and controling a rootkit I’m constantly developing, doing the following:
- Exploiting a vulnerable driver to inject code into the Windows Kernel
- Hide a process by PID
- Hide a process by name (full name > 15 characters)
- Hide a process by name whenever it’s created
- Hide a driver/rootkit
- Elevate privileges from any process given their PID
Finally, I’ll be diving into Virtualization Based Security (VBS) and other defensive techniques to mitigate these attacks.
I’ve been a Red Teamer / pentester since 2011, who have worked in Portugal, Australia, and now at PwC Norway in Oslo. As a researcher I try to publish as often as possible on my Youtube channel, and blog: current & old blog.
My main areas of expertise are reverse engineering, exploit development, and malware development with AV bypass.
Outside of information security, I enjoy spending time with my young toddler and family, editing videos and playing basketball or tennis.
Jeremy Matos
Security helper libraries are often hard to unit test because they should make sure “bad” inputs are not considered valid, but how can we know we are not forgetting one kind of “bad” input? In cases where we don’t have an explicit definition of a good input, Go Fuzzing can be really helpful to gain confidence we are not missing some corner cases.
Using a real-life example of a path traversal vulnerability in Grafana OSS, this talk will show how Go Fuzzing can be used to improve the test coverage of the corresponding security fix. Additionally, it will cover how this technique helped validate more complex security helpers and enabled us to detect some bypasses.
Jeremy Matos is a Principal Security Engineer at Grafana Labs. Rather than breaking things, the former backend developer has shifted his main focus to helping produce secure enough software. He used to work at GitLab and has 15 years of experience in the software security industry. He has given talks at various security conferences, including DEF CON Crypto Village and OWASP AppSec EU.
Pedro Umbelino
Not another hardware hacking talk. This talk is about hacking with hardware. Creative hackers have built their own hardware throughout our (short) history. Today is easier than ever to build your custom purpose hacking gadgets. We will talk about what was built and how can you make your own, by following step by step the motivation and creation of IO433, a custom hardware to hack devices using some well know RF bands.
A full fledged hacker loves to build stuff. Who doesn’t dream to have their own ‘Hollywood’ style hacking gizmo, designed and built by his own self?
In this talk, I will walk a bit down the memory lane and talk about the very first pieces of hardware that were built out of need to hack into something. Alan Turings ‘Bombe’, Blue boxes, Rubber Ducky, ChipSHOUTER and Flipper Zero are some of the examples. Then I will show how hackers with little electronics background can start their own projects, which resources they can use, some tips & tricks, culminating in the analysis of the build process, from simple schematics to fully working prototype.
We live in exciting times, with hardware cheaper than ever, extensive part documentation and almost an online community for every part. It’s the perfect time to start building our own hacking hardware.
Pedro is a security researcher by day and Hackaday contributor by night. He started messing around with computers on a Spectrum, watched the bulletin board systems being dropped for the Internet, but still roams around in IRC. Known by the handle [kripthor], he likes all kind of hacks, hardware and software. If it’s security related even better.
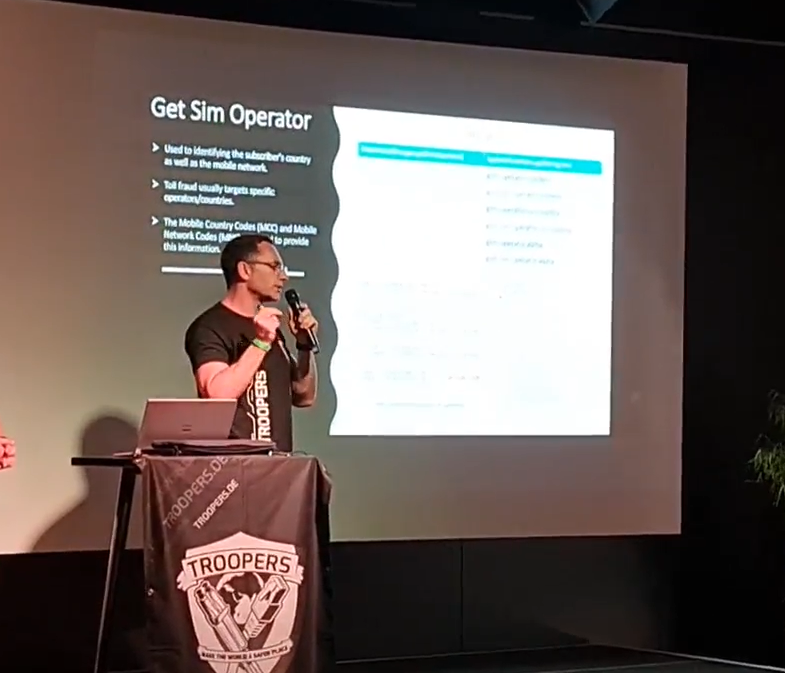

Dimitrios Valsamaras and Sang Shin Jung
The Wireless Application Protocol billing (WAP Billing) is a payment mechanism that enables consumers to subscribe to paid services and get charged directly to their mobile phone bill. To initiate a subscription process the user has to navigate to a website that offers the service, while the device is registered to a cellular network, and click on a designated subscription button. As a verification step, a one-time password is sent to the user which has to be submitted back to the service provider in order to confirm the subscription.
Billing fraud is one of the most prevalent types of Android malware that leverages weaknesses in the aforementioned process in order to automatically subscribe the users to paid services. With revenue reaching up to $10 billion dollars annually, it monopolizes the media spotlight since it found its way to a wider audience through the Google Play Store back in 2017. Up to this day it is still among the Potential Harmful Applications (PHA) with the highest install rate according to Google Play’s transparency report.
This paper focuses on Toll Fraud, a Billing Fraud subcategory and tries to shed some light on its behavioural model from a solid technical perspective. More specifically, we are investigating the evasion techniques used and the actions taken from the malware’s side in order to imitate the user and perform a fraudulent subscription. Finally, we propose improvements with regard to Antivirus detection as well as improvements to the operating system level in order to mitigate the issue.
Full post here: https://www.microsoft.com/security/blog/2022/06/30/toll-fraud-malware-how-an-android-application-can-drain-your-wallet/
Dimitrios Valsamaras: Has participated in many International and local Projects increasing his experience in Mobile, Web and network penetration testing. Holds a degree in Computer Science, with a major in Cryptography and Security. His prior experience in the IT industry spans from development and systems administration to IT Security services. He has a strong passion for reverse engineering and was a member of one of the first reverse engineering research groups in Greece. During the last five years, Dimitrios has been working with some of the largest companies in the industry, including Microsoft and Google, focusing on the Android Ecosystem Security.
Sang Shin Jung: Sang Shin Jung is a Senior Security Researcher at Microsoft. His research interests are focused on reverse engineering and malware research for Android malware, Android applications, and other binaries of Linux or ARM-based system. He is also interested in vulnerability research for various software of mobile devices or embedded system.

Luís Fontes
Github action are being used and abused either in open source projects or in companies. Did you tackle all the security concerns before implementing a deployment pipeline? In this session we will dive into what can go wrong with github actions
After 5 years working with different technologies as full stack developer Luis changed to the AppSec world. Worked at big players like Checkmarx reviewing application’s source code to find and help mitigate vulnerabilities in big players all around the globe. From there to IOVLabs (RSK) and the crypto currency world. Nowadays Luis works at Xapo, a crypto bank.


Pedro Fortuna and Jasvir Nagra
Security isolation is a design principle that improves the resilience of applications against attacks. It works like a second layer of defense that protects the application in the presence of a security breach, by containing the attack to the compromised partition. Sandboxing is one of the techniques often used to provide isolation by restricting code to a limited permission set. Isolation, in this context, is limiting what can happen if a vulnerability is exploited. It has a strong tie to the also well-known security principles of Least Privilege and Privilege Separation.
Any application can and should be designed using these principles. However, it is of vital importance for applications that include untrusted or 3rd party code. Companies can do code reviews of untrusted code before using it, but that is prone to oversights and is too costly to be done for every code change. Additionally, code reviews can be difficult to do in situations where there is no ahead of time access to the code, which is usually the case with web applications, where 3rd party vendor services are directly embedded into applications from their remote servers.
Using 3rd party code/components is a growing trend observed in the last decade, and will keep growing, as companies work towards cutting the development time of new applications. This is especially true for Web Applications as high-scale modern Web Applications use dozens of different 3rd party services. Any untrusted code can be compromised and put the rest of the Web Application at risk, potentially leaking sensitive data.
Throughout the years, several solutions and best practices have been advocated for creating Web Applications leveraging Web Isolation. The core security model of Browser-based apps sits upon the Same Origin Policy (SOP), a mechanism that aims to prevent different security domains from interfering with each other in malicious ways. But the SOP is limited to what it can do and imposes several limitations to how the application is designed. It’s neither practical nor economically efficient to split every code partition in its own origin. Iframe Sandboxing was a good complement to SOP, but its adoption is still anemic, as most third-party scripts require direct access to the DOM and to other scripts in order to function properly. Despite our best efforts to bring effective Web Isolation and privilege separation to the client-side, we are still struggling.
In this talk, we will attempt to tie in the journey of the last 20 years of Web Isolation to the “next 20 years”. We’ll make a pit stop in the present, where we’ll showcase a client-side sandboxing solution that is transparent, does not require any browser modification, and can be embedded into any Web Application. We can pontificate on what will be the likely state of Web Isolation for applications deployed in the future. And lastly, we can discuss where the security challenges will likely be located and how we, the security community, need to work together in order to overcome those challenges.
Pedro Fortuna: Once on a trajectory to a full academic career, where he taught security and computer science courses for about 5 years - ended up falling in love with the fast paced world of entrepreneurship. Started Jscrambler where he leads all security research and drives the company product innovation on application security. Has more than 15 years of experience researching and working on web security. OWASP contributor. Regular speaker in several international security conferences. Main research interests lie in the fields of Application Security, Web Security, Reverse Engineering, Malware, and Software Engineering. Builder of solutions that require code rewriting, sandboxing, or both. Author of several patents in application security.
Recently embraced fatherhood, his biggest and most important project to date.
Jasvir Nagra is widely recognized as a thought leader in software protection. He is co-author of Surreptitious Software, the definitive textbook on software protection, and an early researcher in obfuscation, software watermarking, and fingerprinting. With more than 12 years of experience, his professional path includes companies such as Instart, Dropbox and Google - where he led the Caja project. As an advisor to Jscrambler, he is helping cybersecurity startups address key technological challenges.

Éric Filiol
The recent evolution of malware attack includes more and more data exfiltration. While the market of DLP (Data Prevention) is developing, most of the techniques are still in their infancy and thus are easy to bypass. Then the attacker has to face several critical issues than can trigger alert and block the exfiltration :
- I1. Data may be analyzed so semantic detection (keyword) can be enforced
- I2. Encrypting data before exfiltration is likely to be detected by a simple entropy profile test (however it is rarely in place)
- I3. Encryption means a secret key that can be recovered during static or dynamic analysis
- I4. All outbound traffic may encrypted automatically and this encryption it out-of-control for this attacker
- I5. Known exfiltration techniques (steganography, covert channels) drastically limit the amount of data to exfiltrate without detection (up to a few kilobytes)
- I6. Users’ behaviors may be analyzed to detect suspect actions betraying data exfiltration
This talk intends to show how an attacker could exfiltrate sensitive data while bypassing all these issues by using different innovative malicious cryptography techniques.
These techniques may also be considered by malware designers to make ransomware techniques evolve in a more critical way.
Éric Filiol is a senior consultant in information and systems security, cyber security and intelligence at OPS4SEC, Tallinn, Estonia. He is also professor at ENSIBS, Vannes, France and at National Research University Higher School of Economics, Moscow, Russia in the field of information and systems security. In the last three years he has been in charge of risk and threat assessment of a sensitive private cloud in the Defense sector. He directed the research and the cyber security laboratory of a French engineer school for 12 years. He spent 22 years in the French Army (Infantry/French Marine Corps). He holds an engineering degree in Cryptology, a PhD in Applied Mathematics and Computer Science from Ecole Polytechnique and a Habilitation to Conduct Research (HDR) in Information from the University of Rennes. He holds several NATO certifications in the field of intelligence. He is editor-in-chief of the research journal in Computer Virology and Hacking Techniques published by Springer. He regularly gives international conferences in the field of security (Black Hat, CCC, CanSecWest, PacSec, Hack.lu, Brucon, H2HC, Hacktivity…).
Vítor Ventura
Attackers also have to build infrastructure, and just like defenders they also make mistakes and often don’t secure their own infrastructure. This is one of the reasons why we see a raise in the single-file command and control attack frameworks. This presentation is about two different and apparently unrelated single-file attack frameworks that have more in common than what meets the eye. In fact Alchimist shares the specifications definition of Manjusaka to such a degree that cannot be ignored. The presentation will show two different attackers using the same skeleton to breach defenses and move laterally after they are inside. In the wrap up the presentation will show the attribution pointers that were taken out of the research performed on these two cases.
The presentation will start with a brief introduction of Vitor Ventura. Afterwards it will move the description of the typical architecture user by threat actors. This will set the stage for the single-file attack frameworks that Vitor will be talking about. Next Vitor will speak as if he was a malicious actor and was building a list of specs that he would like to see on a C2 attack framework.In a cadency of one slide per feature (eventually interacting with the audience) he will ask for, multiprotocol, single-file, configurable payloads, encrypted communication, multiple OS, and first stage building options. At this point we have a list of specs for an attack framework. And with this Vitor will start to talk about the first attack framework, dubbed Manjusaka, that he found in the wild with some of these features. He will tell the story of how it was found, its features and its usage in the wild. Based on this he will step into the second framework, Alchimist also found being used in the wild. Do the same kind of description, with an added description of the additional tools found along with this framework. As the presentation nears the end Vitor will establish the parallels between the specs defined by him initially and what was found on the two frameworks. Not only that, but also with the advertisement of features of Manjusaka that were not present in the analyzed samples. Finally Vitor will show that there are clear indications that the specifications for these two attack frameworks seem to have been the same but were implemented by two different sets of developers both being used in the wild. The last slide before the conclusions will show all the possible indicators for an attribution to who might be behind these specifications in an attempt to have the audience draw their own conclusions. The conclusions will alert the audience to the fast deployment capabilities of these kinds of tools, the fast evolution and adoption and the fact that they had the same specifications.
Vitor Ventura is a Cisco Talos security researcher and manager of the EMEA and Asia Outreach team. As a researcher, he investigated and published various articles on emerging threats. Vitor has been a speaker in conferences, like Labscon, Recon, CARO, VirusBulletin, NorthSec, Defcon’s Crypto and Privacy Village, among others. Prior to that he was IBM X-Force IRIS European manager where he was the lead responder on several high profile organizations affected by the WannaCry and NotPetya infections. Before that he did penetration testing at IBM X-Force Red, leading projects like Connected Car assessments and ICS security assessments, custom mobile devices. Vitor holds a BSc in Computer Science and multiple security related certifications like GREM, CISM.
Jb Aviat
Application performance monitoring (APM) is a de facto standard in most software engineering teams. APM solutions help engineers debug distributed services and understand their performance by providing them an extensive visibility over their infrastructure and APIs.
This data is also extremely valuable for attackers, and is available in the context of internal red teams. For example, mapping a service’s attack surface can be vastly improved using APM data. Beyond that, vulnerability discovery, qualification and exploitation can be vastly accelerated.
This is often available to internal teams with no friction since engineering teams already use these tools in production.
This presentation will include the demo an open source Burp Suite plugin (yet unreleased) leveraging APM information to display information related to a request, such as database queries, external network queries, full trace of services called, the versions of the components used… and we’ll see a practical example of exploiting a SSRF leveraging this tool.
Jb Aviat is working on democratising security, bringing AppSec capabilities in the Datadog product. He previously co-founded Sqreen as a CTO. He spent half a decade hunting security bugs at Apple, helping developers solve them, and developing protection used by millions of devices. He has an extensive background in pentesting and reverse engineering.
André Baptista
It all starts with unexpected input. Most modern complex web applications rely on regex for validation and implement input normalization. This includes but is not limited to crucial account identifiers, such as email addresses and usernames.
In this talk, I’ll present the REcollapse technique. I’ve been using it to discover weirdly simple but impactful vulnerabilities in hardened targets while doing bug bounties. I’ll show real-world examples and how to leverage this technique to perform zero-interaction account takeovers, uncover new bypasses for web application firewalls and more.
André (0xacb) is a co-founder at Ethiack and bug bounty hunter. He is also an invited professor at the MSc in Information Security at the University of Porto, coach for the ECSC Portuguese Team and former captain of the xSTF CTF team.
Workshops

Éric Filiol
Most cryptographic challenges are based on either implementation attacks (the key is somewhere in the working environment), mathematical attacks (finding weaknesses in the encryption algorithm) or on poor key management techniques (weak keys or weak key setup).
In this workshop, we deal with a different approach based on a real case. A practical implementation of the Secret Sharing Protocol is presented in which a flaw enables to break the protocol far more efficiently than brute-force.
The different steps are the following:
- The Linux binaries are provided the day before the workshop. The aim is to play the reverse engineering part for anyone interested. A first prize will be awarded to the first attendee which provide the corresponding source code (assembly or C code)
- At the beginning of the workshop the original source code is provided to the audience. The protocol and the code is explained in details (30’ long) The attendees have 20’ minutes to identify the flaw. A second award is given to the first attendee who identifies the flaw.
- Data for the cryptanalysis challenge are given
- The audience tries to find how to exploit the flaw and solve the challenge. A third award is given to the first attendee who solve the challenge or provide significant and convincing method to. (30’)
- The solution is given and presented (20’) and a discussion takes part with the audience on the difference between flaws and backdoors
Awards could be given either during the session of during the BSides Closing ceremony. The awards are provided by the speaker.
Éric Filiol is a senior consultant in information and systems security, cyber security and intelligence at OPS4SEC, Tallinn, Estonia. He is also professor at ENSIBS, Vannes, France and at National Research University Higher School of Economics, Moscow, Russia in the field of information and systems security. In the last three years he has been in charge of risk and threat assessment of a sensitive private cloud in the Defense sector. He directed the research and the cyber security laboratory of a French engineer school for 12 years. He spent 22 years in the French Army (Infantry/French Marine Corps). He holds an engineering degree in Cryptology, a PhD in Applied Mathematics and Computer Science from Ecole Polytechnique and a Habilitation to Conduct Research (HDR) in Information from the University of Rennes. He holds several NATO certifications in the field of intelligence. He is editor-in-chief of the research journal in Computer Virology and Hacking Techniques published by Springer. He regularly gives international conferences in the field of security (Black Hat, CCC, CanSecWest, PacSec, Hack.lu, Brucon, H2HC, Hacktivity…).

Guillaume Lopes
Have you ever used Frida? Do you perform security reviews on Android applications? The objective of this hands-on workshop is to walk you through how to use Frida against Android applications.
During this workshop, we are going to resolve the OWASP crackmes (from level 1 to level 3) using only Frida. The learning outcomes are:
- Set-up your Android environment
- Usage of the common tools for Android analysis (adb, JADX and apktool)
- Learn to create Frida scripts to place hooks on the fly
- Find various solutions for the OWASP UnCrackable Level 1, 2 and 3 applications using Frida
- Usage of Frida against non-rooted devices
The workshop is suitable for pentesters, reversers, malware analysts, and mobile developers who never used Frida.
Guillaume Lopes is a pentester with more than 10 years of experience in different fields (Active Directory, Windows, Linux, Web applications, Wifi, Android). Currently working as a CTO and Senior Penetration Tester at RandoriSec. He also likes to play CTF (Hackthebox, Insomni’hack, Nuit du Hack, BSides Lisbon, etc.) and gives a hand to the Tipi’hack team.